The 2021 RSA Conference, which aims to bring together cybersecurity professionals from around the world to exchange ideas and solutions, was recently held online, and two School of Information teams were among the presenters.
Master’s of Information and Cybersecurity (MICS) student David Ng and lecturer Stuart Schechter presented their research on password managers. A password manager is meant to generate complex passwords and store them to protect your data. However, Ng and Schechter had a hunch most people weren’t using them correctly, and wanted to discover whether these tools were being used as they’re intended.
Spoiler alert: they aren’t.
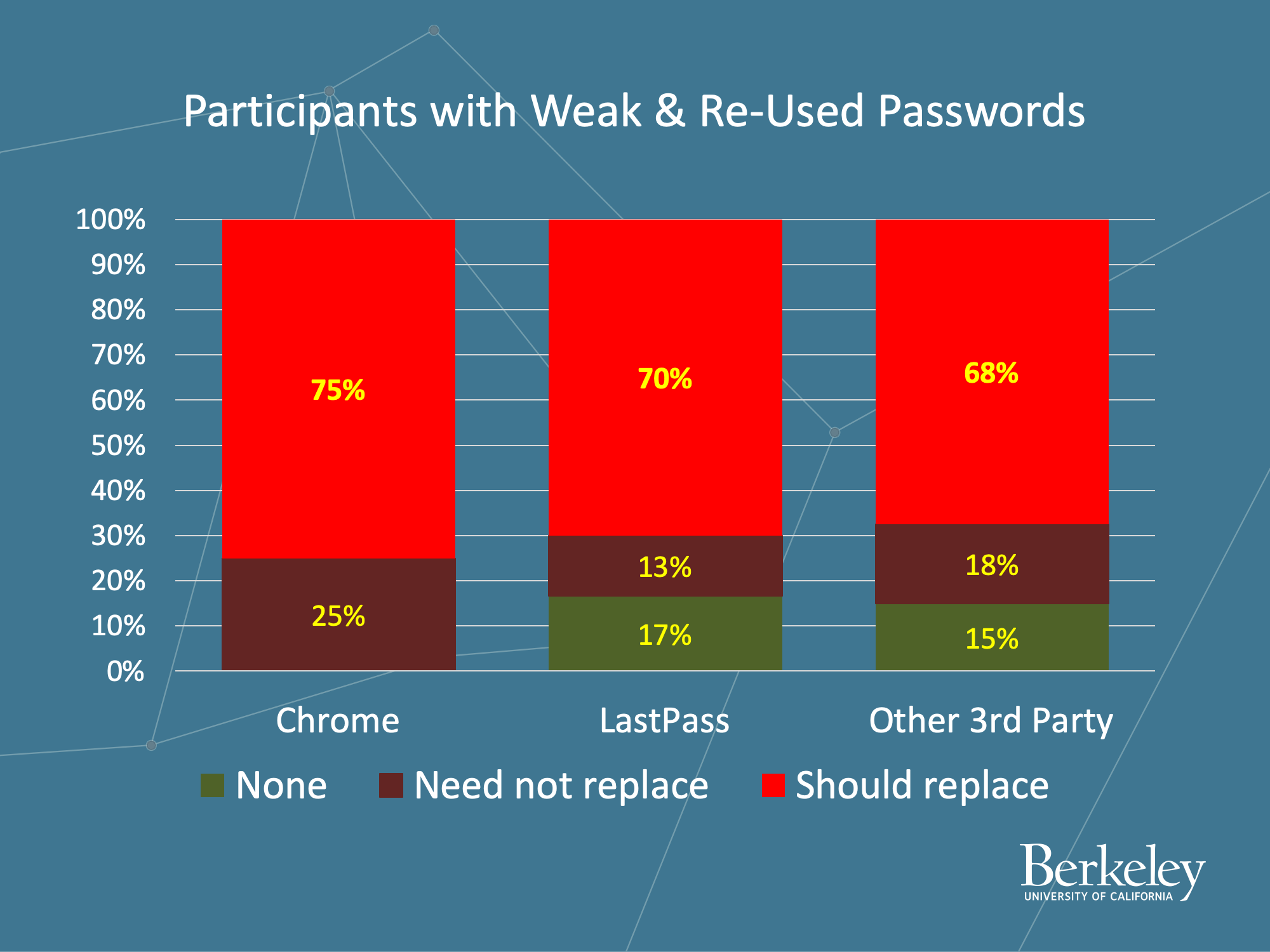
The research, which began as a MICS final project for ‘Usable Privacy and Security,’ involved a study of 100 people who had used a password manager for five months. What they found was that many users simply ignore the password reset notifications suggested by the manager.
“Many users appear to be using password managers without taking advantage of the features necessary to get the security benefits,” Ng said. “We hope our research will remind those giving security advice that they need to tell users not only to use password managers, but to do the work to get the security benefits.”
The pair plan to continue their research and run the study again with some iterations.
MICS students Jasdeep Basra and Tanu Kaushik also presented at RSA. Their session, ‘MITRE ATT&CK® as a Framework for Cloud Threat Investigation,’ presented survey results from research that uncovered the current use of MITRE ATT&CK® in a cloud context, and the challenges and opportunities for improving cloud security and adoption.
The research was a collaboration between McAfee and the UC Berkeley Center for Long-Term Cybersecurity at the School of Information.
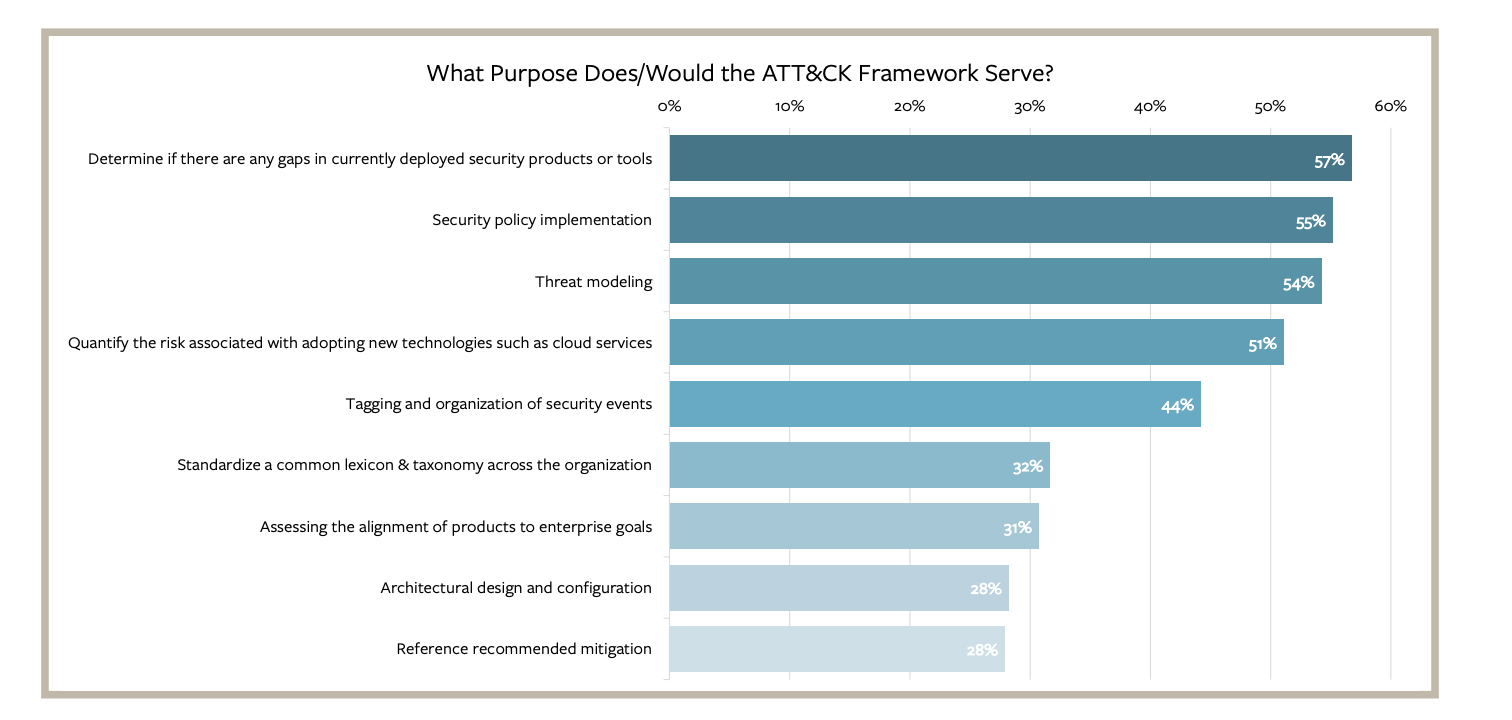
MITRE ATT&CK® is a knowledge base of adversary tactics and techniques based on real-world observations; it’s become a favorite tool of security professionals because it provides a common taxonomy, and offers a matrix of tactics for organizations to deal with identifying gaps in their security products and tools, and spotlights them based on risk.
“The class ‘Usable Privacy and Security’ prepared me by providing knowledge of design heuristics and drafting surveys,” Basra said, “including the use of Qualtrics which we used to draft the survey.”
“The class ‘Managing Cyber Risk,’” Kaushik added, “helped equip us with current cloud security challenges, associated risks and taught us how to conduct interviews with leading security professionals to investigate how they assess and confront these challenges.”
The pair’s study found that 87% of respondents agree that ATT&CK will improve cloud security, and 79% say it would increase their comfort with cloud adoption. Basra commented that, “The information provided in our report is relevant to CISO’s and other security professionals, since many enterprises are moving to utilize cloud computing.” He said that the pandemic accelerated this shift to the cloud, and that it is important to understand how to tackle the security threats that arise in this new era.
“Our comprehensive interviews from security professionals from all backgrounds,” Kaushik said, “from CISOs, CIOs to security architects, penetration testers or governance and risk professionals, ensured we provide insights for a larger information and security community.”
Following the study the team made three recommendations: Use the MITRE ATT&CK Cloud Matrix for threat investigation; employ comprehensive threat investigation; and, embrace automation to reduce the workload of security operations center analysts investigating multiple environments.
Courses like ‘Usable Privacy and Security’ provide opportunities for students to gain the skills needed to design and conduct usability studies on topics of interest, leading to student publications and presentations at security conferences such as RSA. Partnerships with UC Berkeley research centers, like the Center for Long-Term Cybersecurity, further support that research.











